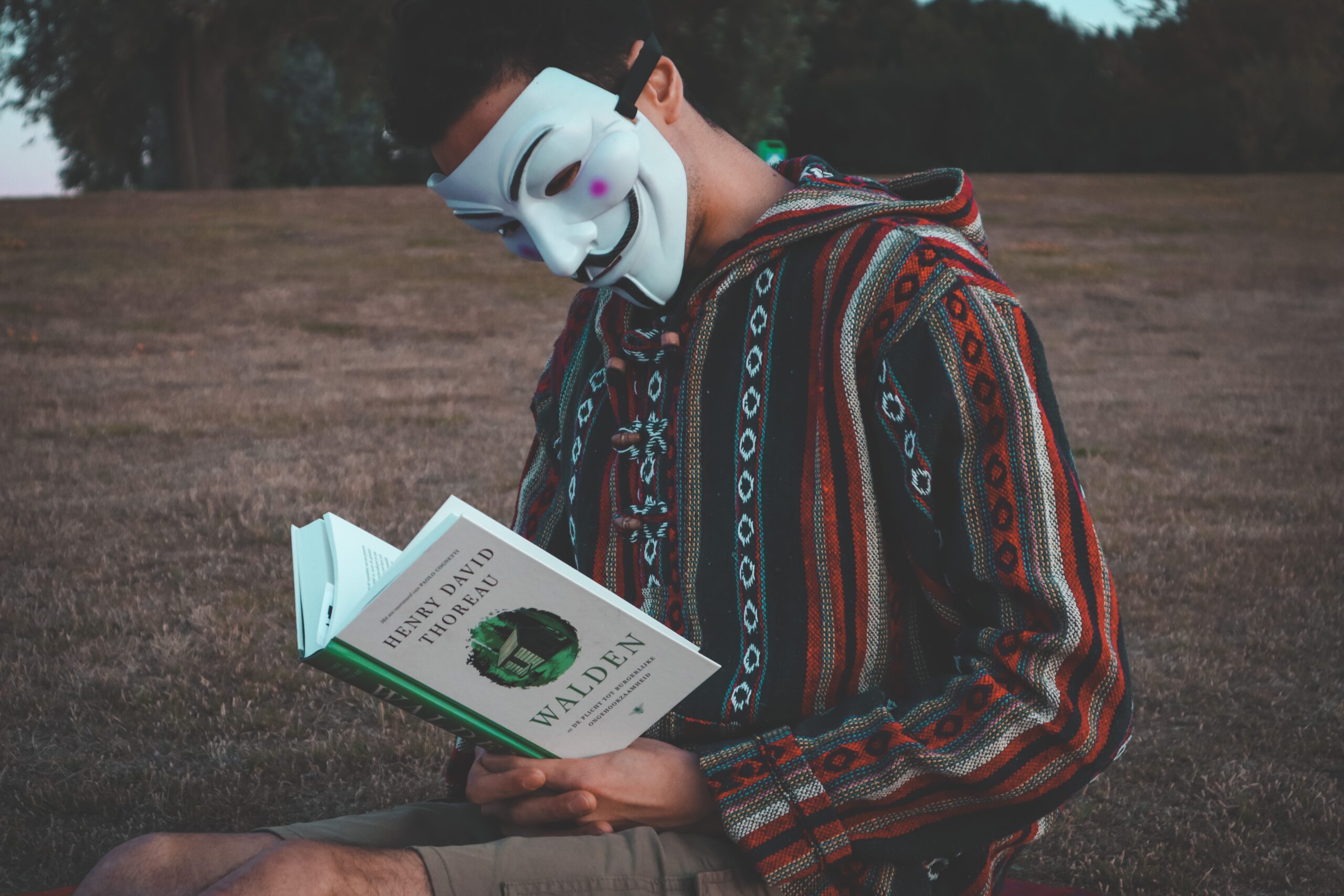
The digital realm has become a battleground for cyber warriors, where hackers wield formidable power to infiltrate systems, expose vulnerabilities, and challenge the status quo. Among these cyber actors, one group has captured the world’s imagination like no other—the enigmatic hackers known as Anonymous.![]()
Operating under the cloak of anonymity, they have left an indelible mark on the world of cyber activism. But can hackers truly be anonymous, or does the digital trail always lead back to their identities?
1. The Myth of Absolute Anonymity
While the moniker “Anonymous” suggests complete anonymity, the reality is more nuanced. Achieving true anonymity on the internet is a complex task, as every digital action leaves a trace that can potentially be traced back to its source.
Hackers may employ various tools and techniques to conceal their identities, such as virtual private networks (VPNs), the Tor network, and encryption. By routing their internet traffic through multiple servers or using encrypted channels, hackers can obfuscate their digital footprints.
2. The Art of Misdirection: Spoofing and Proxies
Spoofing and using proxies are common tactics employed by hackers to divert attention from their true locations and identities. Spoofing involves falsifying data in network packets to make it appear as if the traffic originates from a different source.
Proxies act as intermediaries between the hacker’s device and the target server, making it challenging to trace the connection back to its origin. By employing multiple proxies in different geographic locations, hackers can further complicate attempts to identify them.
3. Decentralization and Collective Action
Hacktivist collectives like Anonymous operate under a decentralized model, which adds another layer of complexity to identifying individual hackers. In such groups, individual members may participate in operations without revealing their identities to one another, relying on public forums and online platforms to communicate.
This decentralized structure makes it challenging for authorities to apprehend hackers, as there is no centralized leadership to target.
4. Slip-Ups and Carelessness
Despite their best efforts to remain anonymous, hackers can still make mistakes or display carelessness that exposes their identities. Whether through technical errors, inadvertent data leaks, or social engineering attacks, hackers can inadvertently leave breadcrumbs that skilled investigators may follow.
Additionally, some hackers may boast about their exploits or seek notoriety, leading to self-identification and potential legal consequences.
5. Hacktivism and Ethical Considerations
Hacktivist groups like Anonymous often engage in cyber activism to promote social justice, transparency, and internet freedom. While some applaud their efforts to challenge oppressive regimes and institutions, others argue that their actions can blur the lines between activism and vigilantism.
The ethical considerations surrounding hacktivism raise questions about the potential impact on innocent bystanders and the potential for unintended consequences.
6. Legal Implications and Consequences
Even with elaborate measures to maintain anonymity, hackers can still face legal consequences if identified and apprehended by law enforcement agencies. Many countries have strict cybercrime laws and extradition agreements, making it possible for hackers to be prosecuted, even if they operate from jurisdictions perceived as hacker-friendly.
7. The Evolving Landscape of Cybersecurity
As technology and cybersecurity measures continue to evolve, so do the methods employed by hackers and hacktivist groups. New encryption techniques, blockchain technology, and artificial intelligence-driven cybersecurity tools may make it even more challenging to trace and identify hackers.
However, law enforcement agencies and cybersecurity experts also continue to develop advanced techniques and collaboration to combat cyber threats.
Conclusion: The Masked Legacy Endures
The question of whether hackers can be truly anonymous remains a captivating enigma in the digital age. While hackers and hacktivist collectives like Anonymous employ sophisticated techniques to conceal their identities, the reality of the digital realm means that absolute anonymity is elusive.
Hackers’ ability to remain anonymous depends on factors such as their technical expertise, operational security measures, and the level of resources and effort invested by those seeking to uncover their identities.
As the digital landscape continues to evolve, the legacy of Anonymous and other cyber actors remains a testament to the complex interplay between technology, anonymity, and the pursuit of digital activism. The masked hackers continue to challenge institutions and promote their vision of an open and just internet, keeping the world intrigued and wary of the ever-evolving digital frontier.