In the vast realm of cybersecurity, the choice of an operating system plays a crucial role in shaping the tools and techniques available to hackers. Linux, an open-source operating system, has emerged as a favorite among hackers for various reasons. In this article, we explore the factors that make Linux an attractive choice for hackers and delve into the features that set it apart in the world of digital mischief.
Open Source Freedom:
One of the primary reasons hackers gravitate towards Linux is its open-source nature. Unlike proprietary operating systems, the source code of Linux is freely available for anyone to inspect, modify, and distribute. This level of transparency empowers hackers with the freedom to tailor the operating system to their specific needs, creating a fertile ground for innovation and customization.
Robust Command-Line Interface (CLI):
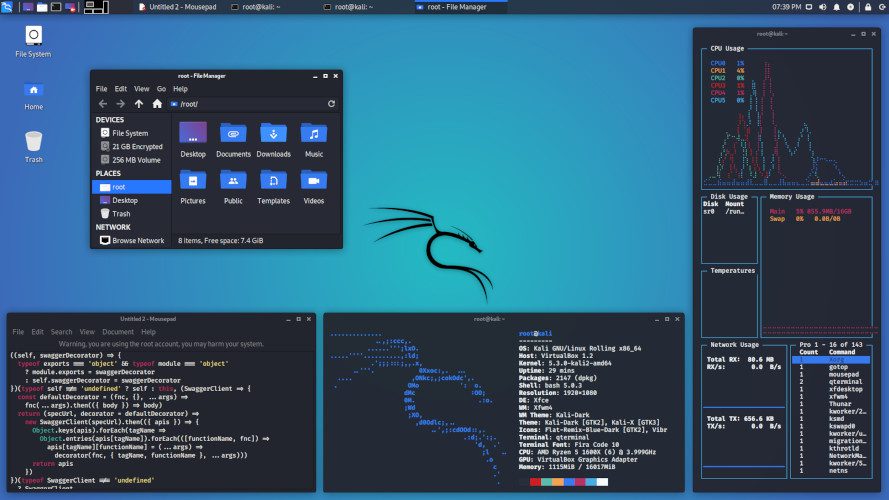
Linux boasts a powerful and versatile command-line interface (CLI) that allows users to interact with the operating system through text commands. For hackers, the CLI provides a streamlined and efficient way to execute tasks, write scripts, and automate processes. The command-line environment also facilitates low-level access to system resources, enabling hackers to delve deep into the inner workings of a system.
Rich Set of Tools and Utilities:
Linux comes equipped with a vast array of built-in tools and utilities that cater to the needs of hackers. From networking tools for reconnaissance to security utilities for penetration testing, Linux provides a comprehensive toolkit for those looking to explore vulnerabilities and exploit weaknesses in digital systems.
Stability and Reliability:
Linux is renowned for its stability and reliability, making it an attractive choice for hackers engaged in prolonged and intricate tasks. The robust architecture of Linux ensures that the operating system remains responsive even under heavy loads, contributing to a seamless and dependable hacking environment.
Customization and Flexibility:
Hackers value the flexibility and customization options that Linux offers. With various distributions (distros) available, each catering to specific needs, hackers can choose an environment that aligns with their preferences and objectives. This flexibility extends to the desktop environment, kernel modules, and system configurations, providing hackers with a tailored platform for their activities.
Community Support and Collaboration:
The vibrant and active Linux community is a significant draw for hackers. The collaborative nature of the community fosters knowledge sharing, troubleshooting, and the development of new tools. For hackers, this communal atmosphere provides a valuable resource for staying updated on the latest trends, sharing insights, and accessing a wealth of collective knowledge.
Security Features and Permissions:
Linux incorporates robust security features, including a strict user permission model. Each user is assigned specific permissions, limiting their access to system resources. The principle of least privilege ensures that even if one user account is compromised, the potential damage is mitigated by the restricted permissions. Additionally, Linux’s security modules, such as AppArmor and SELinux, provide enhanced access controls, confining processes and minimizing the attack surface.
Anonymity and Privacy Features:
For hackers navigating the digital landscape, Linux offers features that enhance anonymity and privacy. Distros like Tails and Whonix, built on the Linux foundation, prioritize user privacy by routing internet traffic through anonymizing networks like Tor. This emphasis on privacy aligns with the interests of hackers looking to mask their digital footprint.
Target Variety and Compatibility:
Linux is prevalent across a diverse range of systems, from servers and embedded devices to desktop computers. This ubiquity makes it an attractive choice for hackers who need a versatile platform capable of adapting to different target environments. The compatibility of Linux with various architectures and hardware configurations allows hackers to broaden their scope and target a wide array of systems.
Conclusion: The Linux Advantage in Hacking
In the intricate dance between cybersecurity defenders and hackers, the choice of operating system plays a pivotal role. Linux, with its open-source philosophy, powerful command-line interface, rich toolkit, stability, customization options, community support, security features, and compatibility, stands out as a preferred tool in the hacker’s arsenal. While ethical hacking aims to fortify digital systems, the same features that attract cybersecurity professionals to Linux also make it an alluring choice for those seeking to exploit vulnerabilities. Understanding the factors that make Linux a hacker’s favorite sheds light on the dynamic landscape of cybersecurity and the tools employed by those navigating its intricate terrain.