Whenever everything is digital, and Covid-19 provides a boost to the digital market, every piece of paperwork or routine labor transfers to the technological realm, and hacking is rampant, the world is a safer place. Hacking is becoming more popular, both legally and criminally. It not only aids in the protection of data from opponents or illegal hackers. Kali Linux is a platform that assists hackers.
What is Kali Linux?
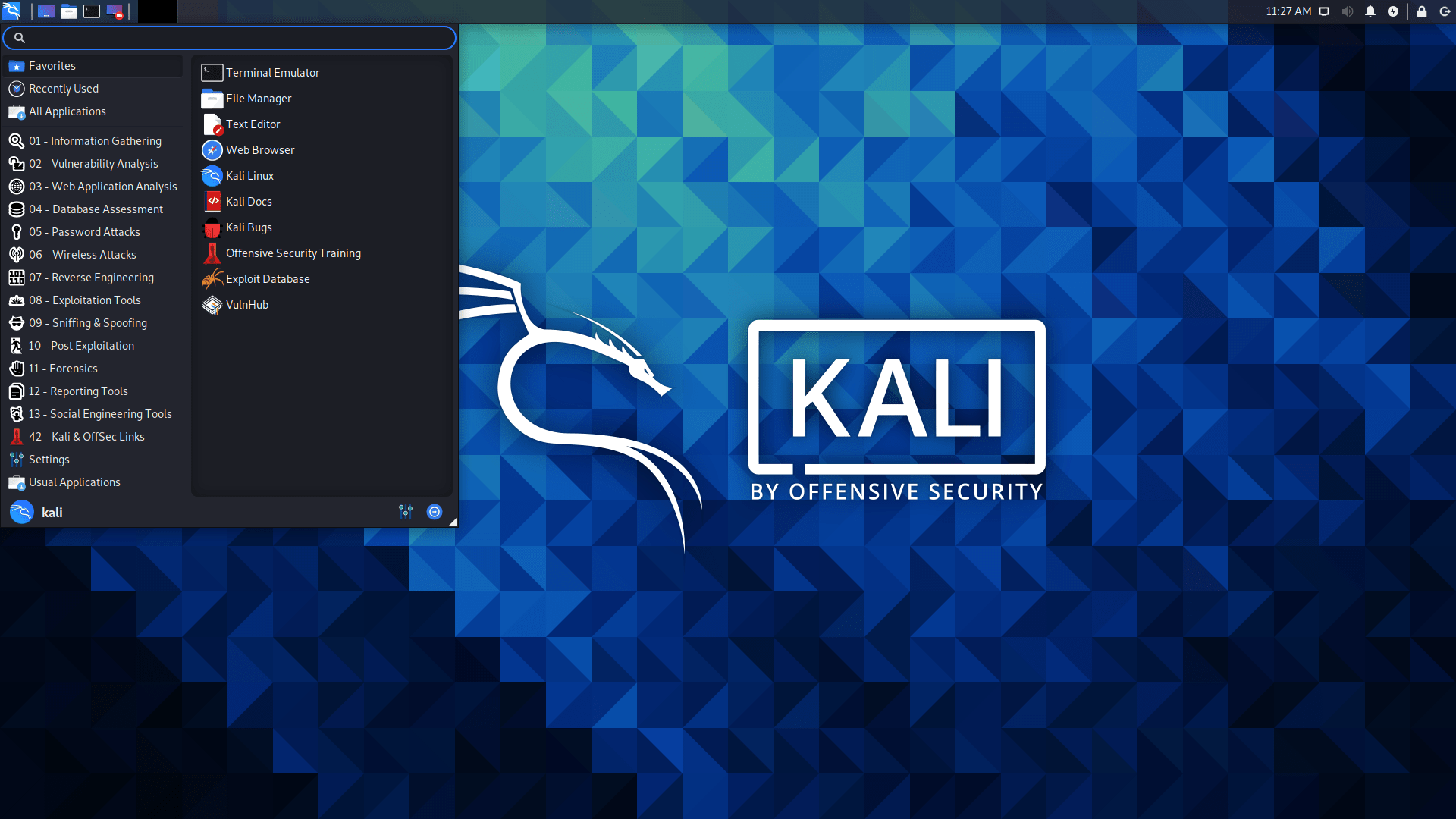
The Debian-based Kali Linux operating system is a fork of the popular Linux distribution. It is a precisely constructed operating system tailored exclusively to the needs of network analysts and penetration testers. With the inclusion of a myriad of pre-installed tools with Kali, the operating system transformed into an ethical hacker’s Swiss Army knife.
When it comes to sophisticated penetration testing and security auditing, Kali Linux is the preferred operating system. Kali is a collection of several hundred tools designed to assist with various information security tasks, including penetration testing, security research, computer forensics, and reversing engineering projects. Kali Linux is not inherently unlawful in and of itself. After all, it is just an operating system. This software is also used for hacking, and when someone uses explicitly it for hacking, it is considered illegal.
Why Do Hackers Use Kali Linux as Their Operating System?
The Linux operating system Kali Linux is one of the most popular operating systems for hacking. Other Linux operating systems, such as BackBox, the Parrot Security operating system, BlackArch, Bugtraq, and Deft Linux (Digital Evidence & Forensics Toolkit), are also popular among hackers. Hackers primarily employ it because of its attractive and distinguishing characteristics. Hackers might even operate in their native languages as a result of this. Kali is nothing more than a Linux operating system with hacking tools pre-installed.

Operating systems other than Windows and Mac can be used to run this Operating system as well. Several hundred tools are included in Kali, all of which are geared toward various information security tasks such as Penetration Testing, Security Research, Computer Forensics, and Reverse Engineering, which attracts the most Hackers. The Kali Linux system is aimed at security; it is primarily famous for Testing Security Reasons on various kinds of equipment. It is used by both white hat and black hat hackers, and it is available for free download.
As a follower of the Backtrack philosophy, Kali Linux is much more advanced and has more features. In a wireless AP, Kali can hack many different types of networks, including WEP, WPA, WPA2 security, and many more types of network security. It also aids in the development of information technology abilities, which allows hackers to become more professional in their area.
I’m interested in hacking can anyone help me?
Me puedes recuperar mi cuenta de FB
Hackers use Kali Linux for only one reason. This is the simplest system for ethical hacking. No matter what manual you look at, it is used exactly the way it is easiest, using another system the user simply will not understand it and he will not succeed. I used Kali Linux, Ubuntu, Blackarch and just Archlinux. Kali Linux was my first system in a Linux environment. Kali is really beautiful, but I stopped my eyes on Arch linux. I think all Kali Linux owners know how it can take out the brain with its dependencies. Or after a full upgrade, it will break down altogether so that you will have to install it again. So my opinion is that half of the post is true, and half is false.