Encryption is the process used to store data in the encrypted form. Encryption standards have been used form many years. Since ancient time, people are using that kind of encrypted language for communication.
The reason behind using encrypted language is to secure data in a more encrypted form. The ancient kings were also used this encrypted language to hide their wealth.
The best example of ancient encryption language is the Voynich Manuscript. No person can decode this language because there is no key left for decode.
 Computer encryption is the same as in ancient times. One key for encoding and other for decoding. Now the latest encryption standards are 128bit and 246bit. Below is the detailed analysis of encryption standards.
Computer encryption is the same as in ancient times. One key for encoding and other for decoding. Now the latest encryption standards are 128bit and 246bit. Below is the detailed analysis of encryption standards.
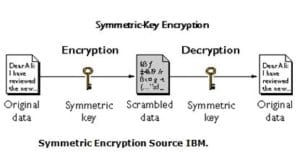
Symmetric Encryption: In symmetric encryption, there is only one key is used to lock or unlock the data. The same key will for the sender and receiver.
Advantages:
- Symmetric key encryption doesn’t require as many CPU (Central Processing Unit) cycles as asymmetric key encryption, so it is generally faster.
- When you transfer data to other people if by mistake hackers intercept your data half of its path since there is no key transmitted with the data, the chances of data hacking will be zero.
- Symmetric encryption uses password authentication to prove the receiver’s identity.
- In symmetric encryption only secret key decrypt data.
Disadvantages:
- The first disadvantage is, the sender has to share its private key with the receiver.
- If the receiver doesn’t have a private key he cannot decrypt data.
- If hackers stole the key from the sender system, they can easily decode that information.
- It cannot provide digital signatures that cannot be repudiated.
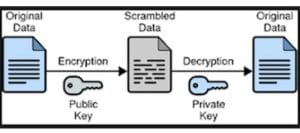
Asymmetric Encryption: It is slightly different from Symmetric encryption. In asymmetric encryption, two different keys used for encryption and decryption. For example, when you send a mail to your friend on Gmail, the public key is required for encrypting the message. From the other side, if your friend wants to read your message, the private key is necessary to him for decode.
In this scenario, the sender and receiver don’t need to share private or public keys with each other. All conversations will be automatic between both systems. Chances will be zero for the attackers to decode your conversation.
Advantages:
- The main advantage is of this encryption, there is no need for exchanging keys, that eliminating the key distribution problem.
- It increased the data security level. The private key will never be transmitted or revealed to anyone.
- It can provide digital signatures for authentication and non-repudiation.
Disadvantages:
- There is only one disadvantage of this encryption, its automatic process and take time to encrypt and decrypt data. So it’s a bit slower than symmetric encryption.
This the main difference between the two highly used complex algorithms. In our next session, we will discuss encryption software.
best pART
Preciso descifrar esse código 369
Saya ingin masuk menjadi member
Ada yg bisa bantu sya hack akun fb sya
I want to learn hacking
i want to join anoymous
Üye olmak istiyorum lütfen